Automated Penetration Testing That’s Faster, Smarter and More Affordable
Backed by Kaseya and powered by Vonahi Security, vPenTest gives you full-scale, enterprise-grade network penetration testing - without waiting weeks for consultants or paying premium prices.
Instantly Uncover Network Risks with Automated Pen Testing
Run real-world simulated attacks - no consultants, no delays.
Pen Test Your Network in Minutes - Not Months
Click. Scan. Secure. vPenTest automates what used to take weeks.
Know Where You're Vulnerable - Before the Attackers Do
Automated penetration testing that delivers clear, actionable results.
Ditch the Consultants. Run Your Own Pen Test.
vPenTest gives you control, speed, and real results — without the wait.
Hackers Work 24/7 - So Should Your Defenses
If an attacker came knocking tomorrow, would your network hold up? vPenTest helps you find out - before they do.

Complete Flexibility
Easily schedule internal or external network penetration tests whenever your organization requires them.
Cost Effective
Save over 60% compared to traditional or manual network penetration testing.
Become Compliant
vPentest is fully compliant with industry standards, including PCI, HIPAA, SOC 2, and cyber insurance requirements.Launch internal or external penetration tests on-demand - anytime you need them.
- Goes far beyond basic vulnerability scans - simulates real-world attack paths.
- Save 60% or more compared to traditional manual pentests.
- Monitor progress in real-time as the test unfolds across your network.
- Built to support compliance with PCI, HIPAA, SOC 2, and cyber insurance requirements.
- Backed by veteran consultants with OSCP and OSCE certifications and 10+ years of offensive security experience.
Put Your Network to the Ultimate Test
Find your weaknesses before a real attacker does
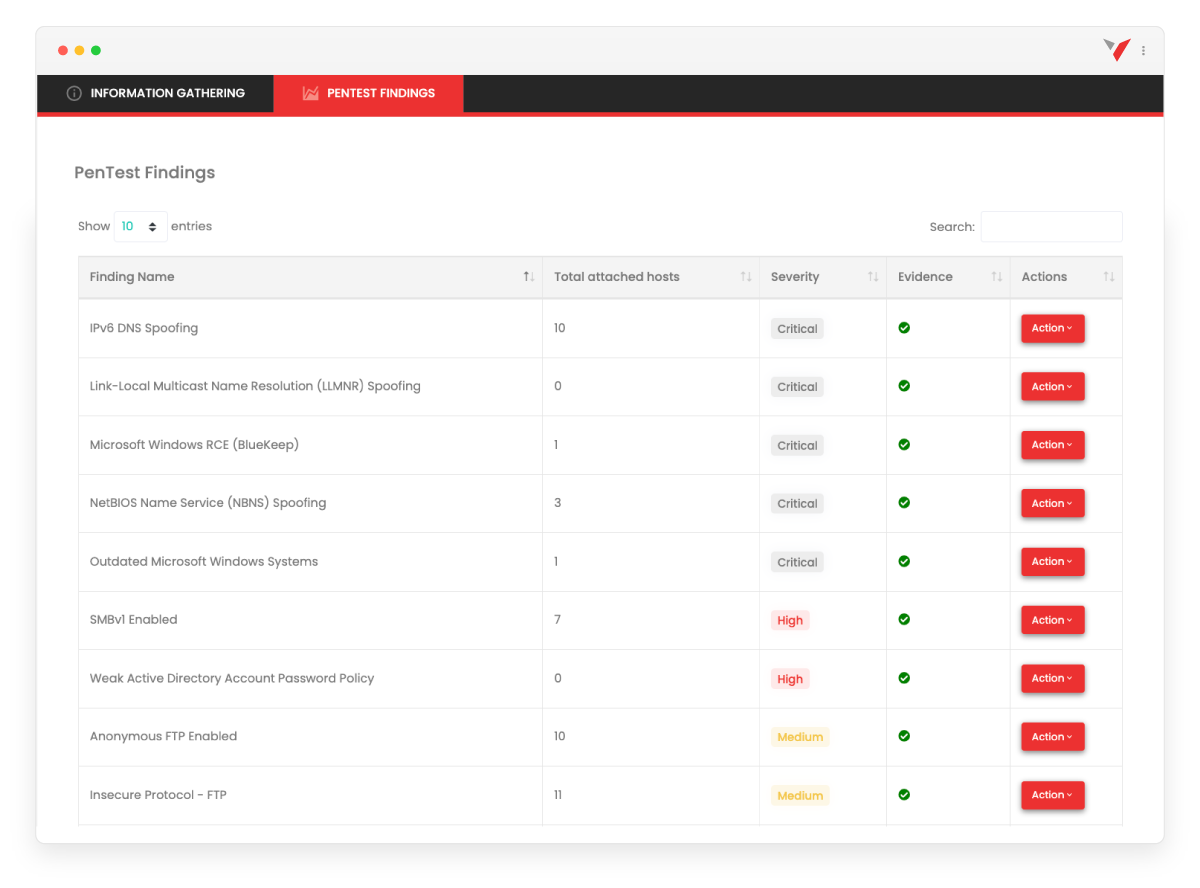
vPenTest acts like an ethical hacker inside your network - simulating real-world attack scenarios to show you exactly what’s at risk. It doesn’t just list vulnerabilities; it actively exploits them to reveal how a breach would unfold: discovering sensitive data, escalating privileges, capturing credentials, and moving laterally just like a real threat actor.
You’ll see your environment the way an attacker would - before they ever get the chance.
Modern PenTesting. Built for Today’s Threats.
Vonahi Security (a Kaseya company) has reimagined network penetration testing with vPenTest - making it easy, fast, and cost-effective for security-conscious teams that want real protection without the red tape.

Affordable. Accurate. On-Demand.
vPenTest is a full-scale, automated penetration testing platform that replicates the tools, techniques, and methodologies used by expert consultants - all in one powerful SaaS solution.
Built on a continuously evolving framework, vPenTest delivers faster, more consistent, and cost-effective assessments without the risk of human error. It’s penetration testing modernized - delivering enterprise-grade accuracy at a fraction of the time and cost.
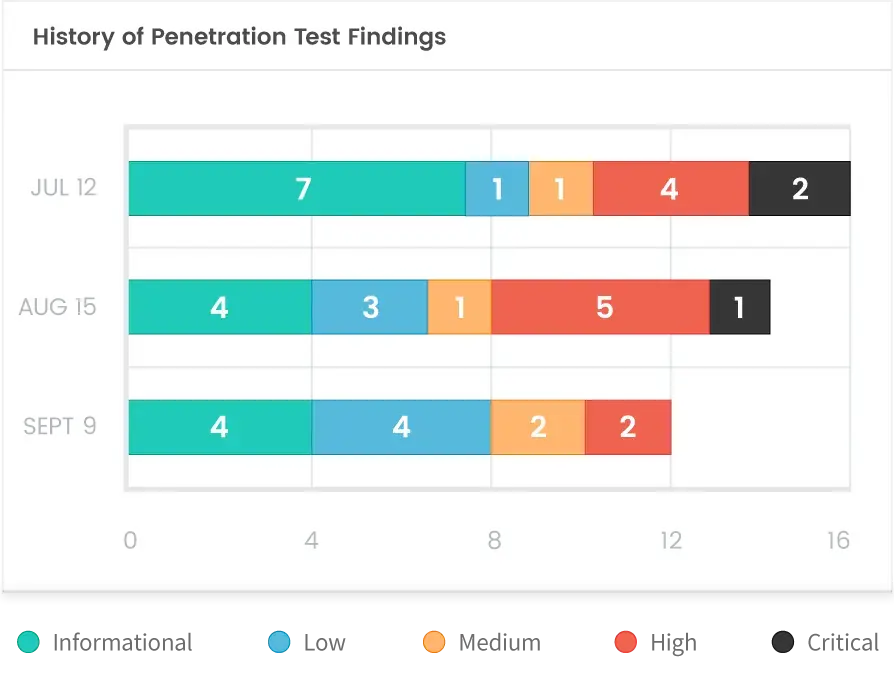
Stay Ahead of Threats with Ongoing Testing
Run network penetration tests monthly — or anytime new risks appear. With vPenTest, you can launch a test in minutes and monitor your organization’s risk posture in near real time.
Each report includes trend data, so your team can clearly track security improvements month over month.
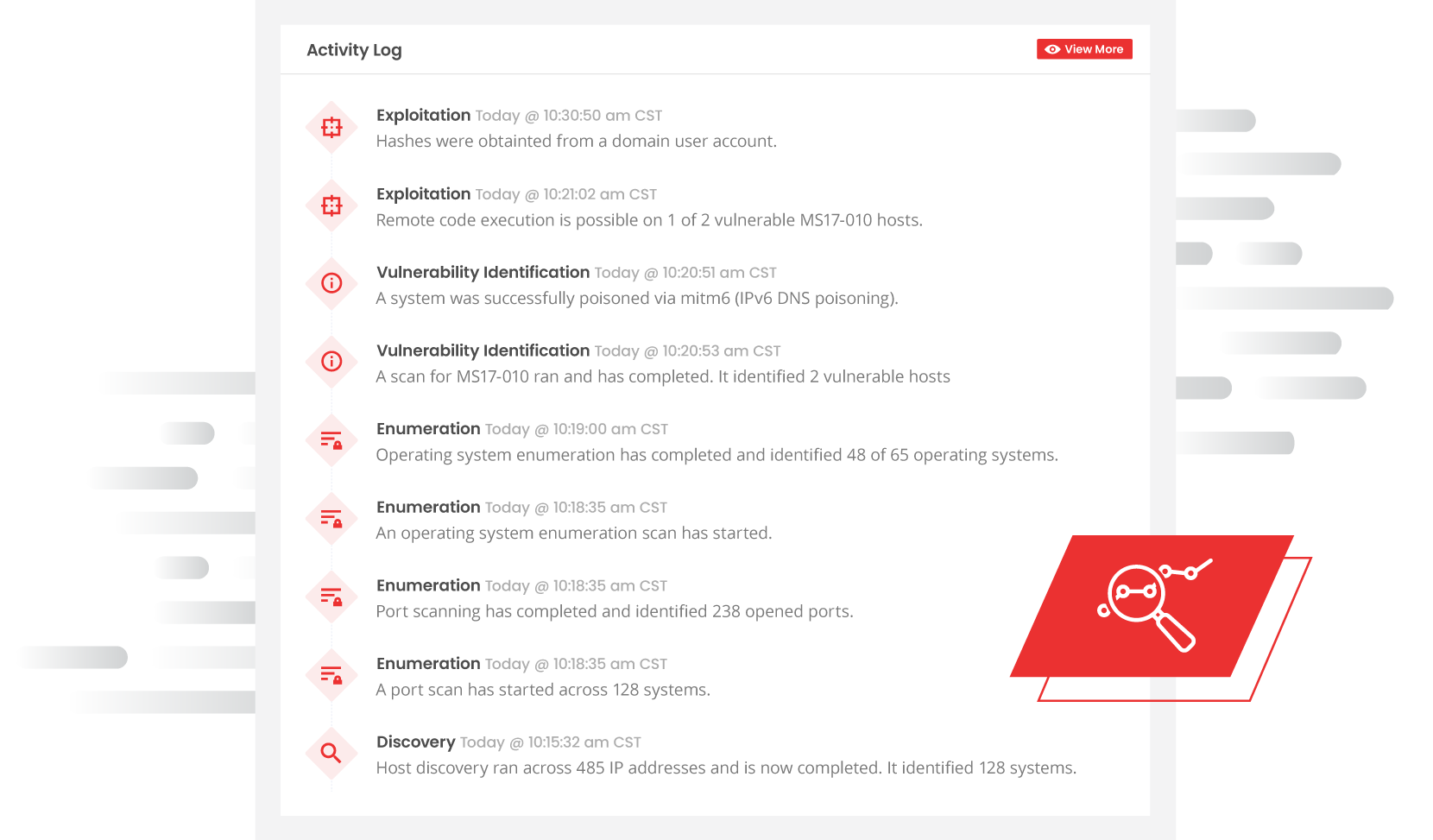
Real-Time Visibility
Get instant insight into every action taken during the test.
vPenTest’s real-time activity logs integrate seamlessly with your SIEM and incident response processes - so you can monitor each step, detect blind spots, and validate your security controls as the test unfolds.
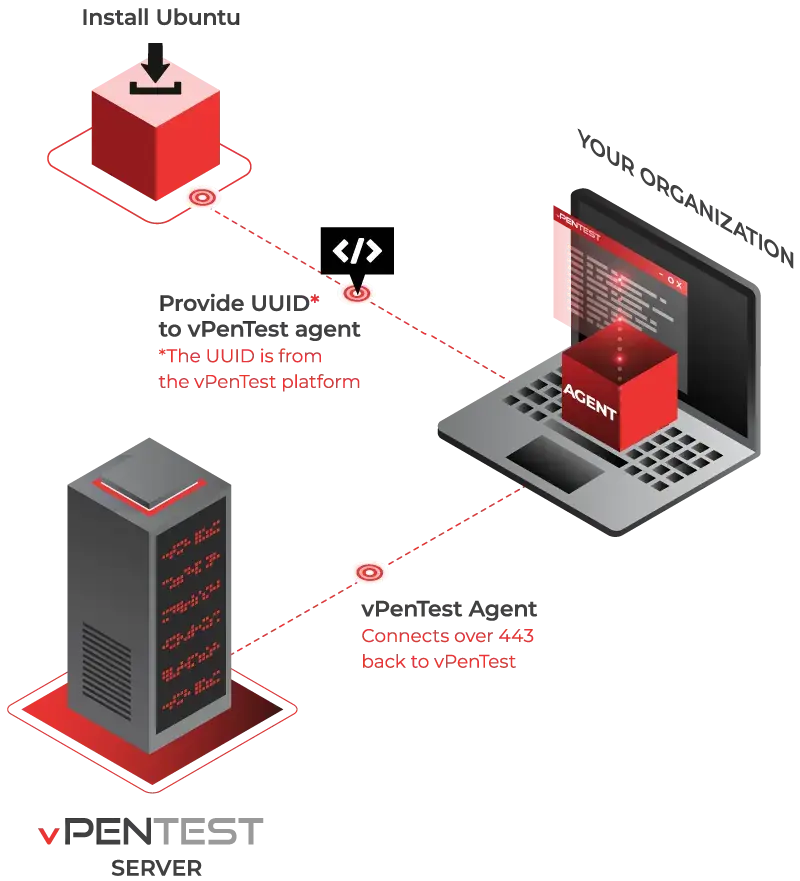
Save Time & Stay in Control
Deploy the agent, launch your internal assessment, and receive detailed results in just days. You set the pace - control when, how often, and where each test runs. No consultants, no delays. Just deploy, click, and go.
Red Team on Demand
Tap into elite-level expertise - without the overhead.
vPenTest gives you the power of a certified Red Team at your fingertips. Backed by eCPPT, OSCP, and OSCE-certified professionals with decades of real-world experience, it delivers true network penetration testing - on your schedule, at a fraction of the cost.
Move fast. Stay secure. Think like a hacker.
Get Clear, Actionable Reports - Fast
vPenTest delivers a detailed, easy-to-understand report within 48 hours of completing your test - so your team can review findings, prioritize fixes, and take action without delay.



vPenTest Eliminates the Hassles
of Traditional Pen Testing
Finding a qualified penetration testing vendor is often slow, inconsistent, and expensive.
vPenTest has engineered a better way.
❌ The Traditional Approach is Broken
Organizations often struggle with:
- Waiting weeks just to find an available vendor
- Evaluating consultant credentials to ensure they’re qualified
- Dealing with poor communication and limited knowledge transfer
- Receiving vulnerability scans disguised as pentests
- Getting incomplete or unclear reports that don’t explain impact or remediation
✅ vPenTest Solves All of That
Vonahi's platform delivers:
- On-demand availability: no scheduling delays
- Expert logic built-in: no need to vet consultants
- Clear, actionable reporting for both technical and executive audiences
- Real penetration testing, not just scanning
- Remediation guidance that’s both strategic and technical
Vonahi has spent the last five years perfecting vPenTest ... and it’s only getting better.
ON-DEMAND RISK MANAGEMENT
Move Beyond Point-in-Time Testing - Assess Security Monthly
Traditional penetration tests offer only a snapshot in time. With vPenTest, you can run full-scale network penetration tests monthly or on demand - giving you near real-time visibility into your cybersecurity posture.
The platform simulates real-world attacks to validate the effectiveness of your existing controls, identifies gaps, and helps you prioritize remediation - all while minimizing operational risk.
COMPLIANCE READINESS
Stay Compliant - With More Flexibility and Real-Time Visibility
vPenTest makes it easy to meet compliance requirements with flexible scheduling and real-time visibility. You can run tests on demand, track activity as it happens, and validate network segmentation. Beyond compliance, it also identifies gaps that fall outside security best practices.
ALWAYS BE IN THE KNOW
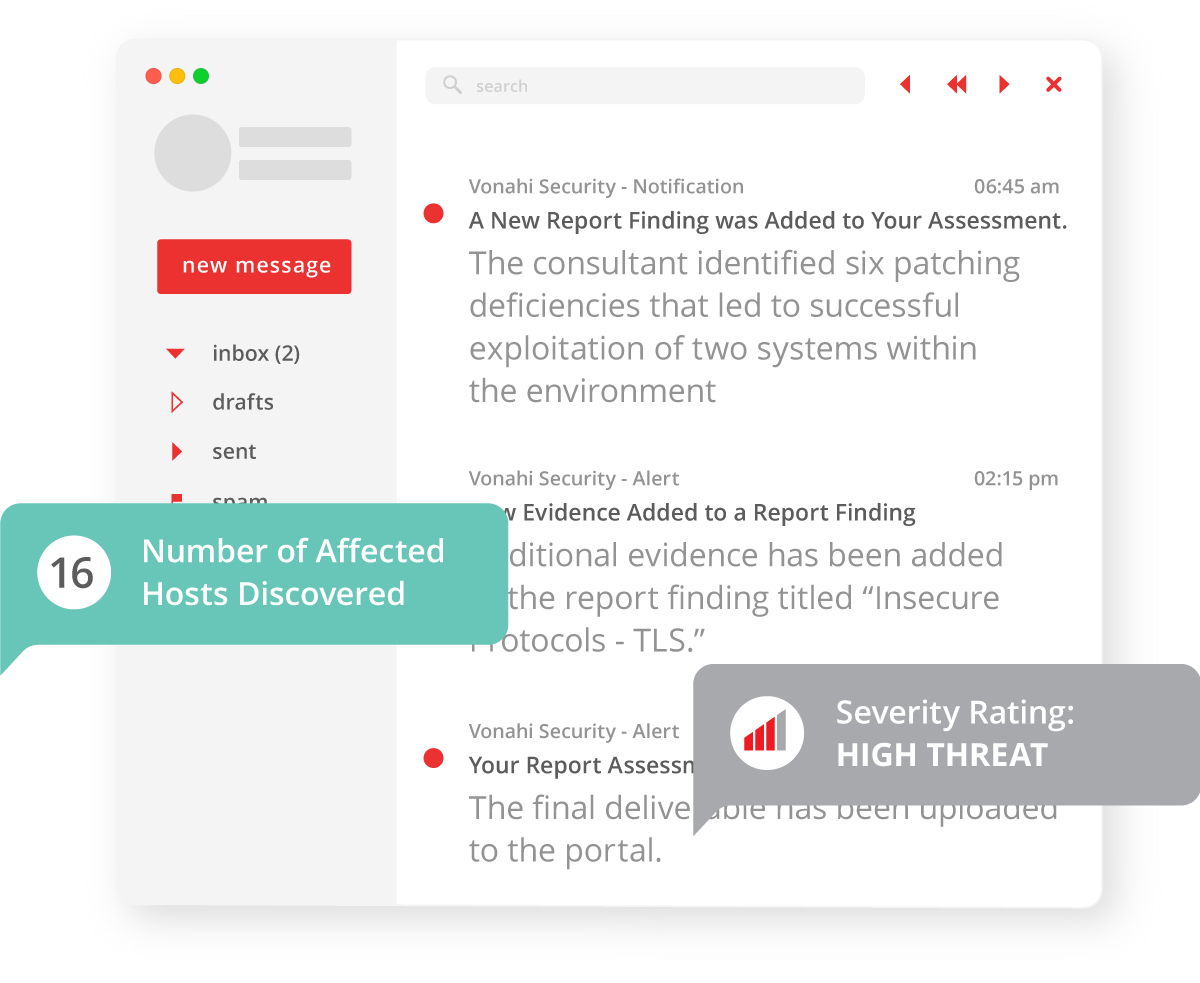
Track the Progress and Results of Your Penetration Test in Real Time
vPenTest includes a real-time progress tracker that keeps your IT team informed at every stage of the engagement. You'll know exactly what phase the test is in, when it’s expected to complete, and see any preliminary findings as they’re uncovered. With full visibility into ongoing activities, your team is never left in the dark.
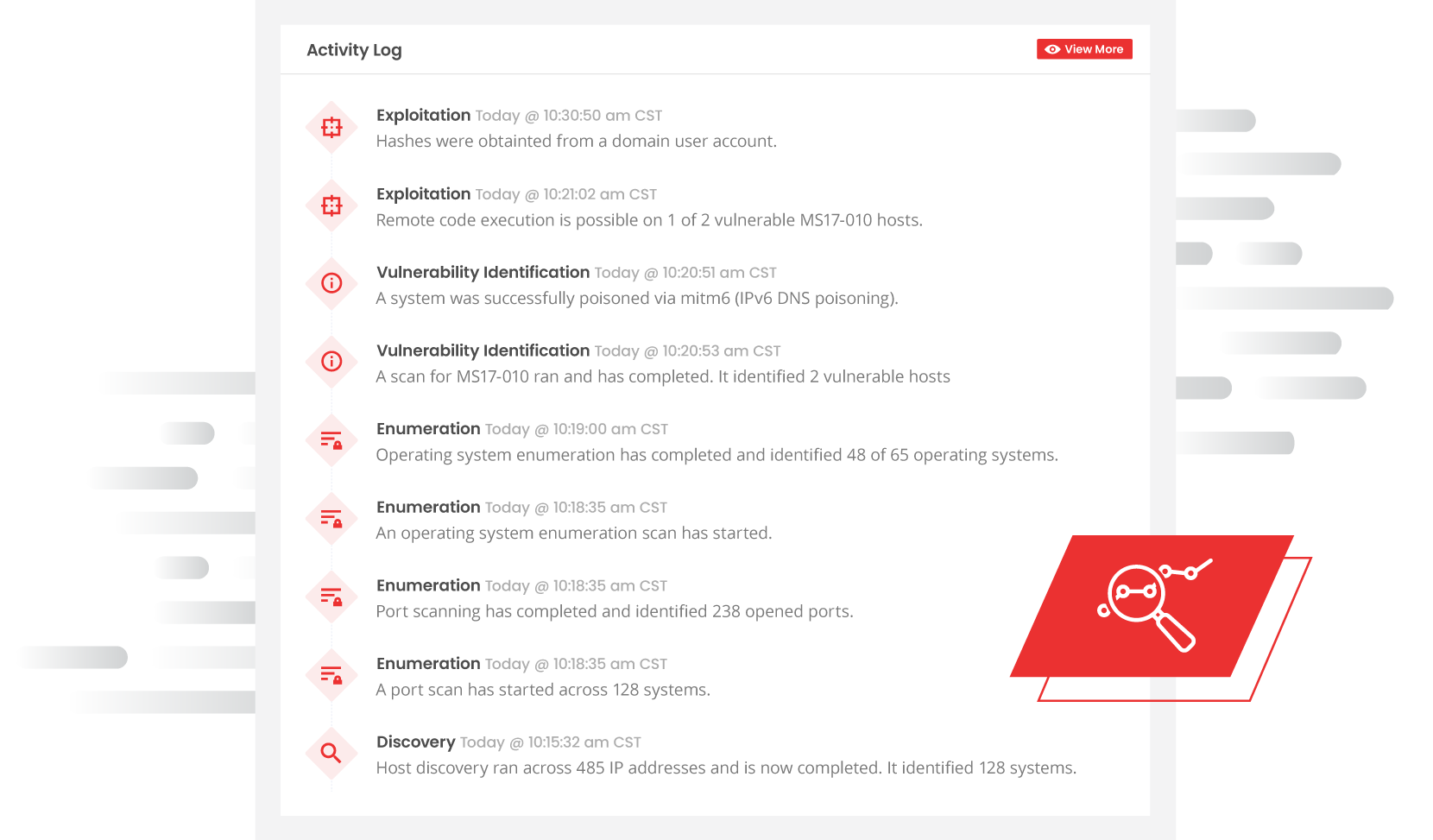
VALIDATE YOUR SECURITY CONTROLS
Ensure Your Security Controls Are Working with the Activity Log
vPenTest includes a detailed activity log that tracks every action taken during the penetration test, allowing your team to validate detection and response capabilities in real time. By correlating vPenTest activity with your SIEM and incident response processes, you can assess how well your security controls are performing. Every engagement becomes a practical, low-risk purple team exercise — strengthening both your defenses and your visibility.
PRE and POST-BREACH SIMULATION
vPenTest allows you to run both pre- and post-breach attack simulations at any time across your internal and external network environments. This provides a comprehensive view of how an attacker could gain initial access - and what they could do next if successful. With on-demand testing, you can evaluate your defenses from every angle, whenever needed.

vPenTest performs Open Source Intelligence (OSINT) Gathering by collecting publicly available information (such as employee names, email addresses, and other data) that could be used to support an attack.
It then conducts a Host Discovery to identify active systems and open ports within the target environment.
Following this, the platform carries out an Enumeration, analyzing discovered services and systems to uncover valuable details and potential vulnerabilities for further exploitation.
vPenTest uses data gathered during the OSINT, host discovery, and enumeration to launch targeted exploitation attacks against vulnerable services. These include password-based attacks, man-in-the-middle (MitM) attacks, relay attacks, and other real-world techniques.
After gaining initial access, post-exploitation begins, where vPenTest automatically attempts privilege escalation and evaluates new attack paths to determine whether deeper access or exposure of sensitive data is possible.
Hackers Don’t Sleep - And Now, Neither Does Your Network Security
If your organization was targeted tomorrow, would you be ready? With vPenTest, you’ll find the gaps before attackers do — and be able to fix them fast.
Network penetration testing simulates a real-world cyberattack to identify vulnerabilities and weaknesses in your IT infrastructure - before a malicious actor can exploit them.
Think of it as a controlled, ethical hack that helps your organization uncover and fix security gaps proactively. The goal? Strengthen your defenses, reduce risk, and stay one step ahead of attackers.
vPenTest replicates the exact steps a professional penetration tester would perform during a live assessment - but with the speed, consistency, and scalability of automation.
It executes a full kill chain, including:
- Service enumeration
- Vulnerability analysis
- Exploitation and post-exploitation
- Privilege escalation
- Lateral movement
- Documentation and reporting
Built by certified experts with 10+ years of real-world experience, vPenTest integrates the tools, tactics, and logic of seasoned consultants into a streamlined SaaS platform — delivering reliable, repeatable, and high-value results every time.
A vulnerability assessment identifies known weaknesses in your network - but stops there. It doesn’t test how those vulnerabilities could be exploited or what damage they could cause.
vPenTest goes further. It not only detects vulnerabilities, but also simulates real-world exploitation and post-exploitation scenarios — just like a human attacker would. This shows you the actual risk and impact of each vulnerability, such as access to sensitive systems or data leakage, giving you the context needed to prioritize remediation effectively.

